Watch an episode of NCIS or CSI and you might get the impression that hacking electronic devices is a simple way to learn all you need to about a person. While these shows tend to gloss over the science of the forensic work, the truth is, most electronic devices only rely on obscurity to keep data safe. Here is an article from Cambridge researchers discussing how to read contents using lasers (but not feverish typing on a keyboard for software that is clearly graphical in nature.). That sound crazy right? Don’t forgot Princeton has guidelines on security based on the fact you can freeze RAM to extend its retention.
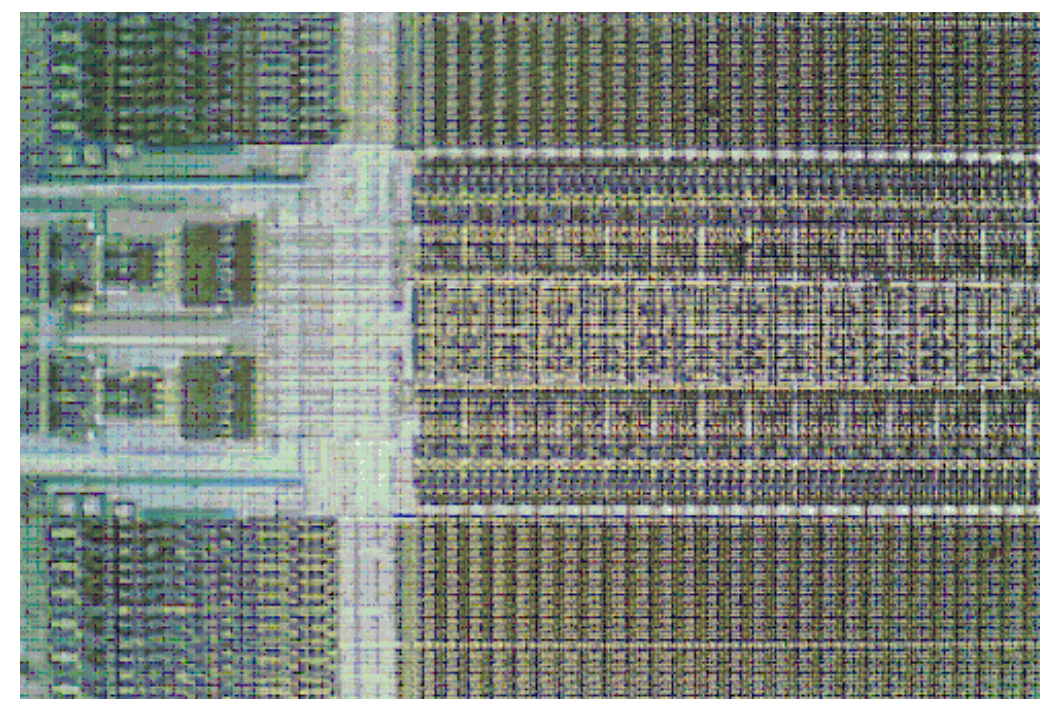
Techniques like these might not work much longer. This new SRAM chip from Maxim, the DS3660, isn’t big but it is continuously updating its cells to prevent a recoverable data pattern from being imprinted. Tamper-resistant features will work to keep the secrets of the chip safe, should someone try TV-style hacking techniques.
Additionally, it also includes cool features like a 64-bit unique serial number, a random-number generator, and a seconds counter all while supporting I2C communications.
Check with Maxim for more details. Don’t be surprised if samples are tough to come by….: http://www.maxim-ic.com/datasheet/index.mvp/id/6767